I find USPS Informed Delivery very helpful for letting me know about mail and packages I should receive. So when I saw a USPS Informed Delivery email in my Junk folder, I figured it must be a mistake so I moved it to my Inbox. It said I had missed a package. I received a package recently and it was a couple days late, so I thought maybe the site just didn’t get updated that it had been delivered. I clicked on the link to review the tracking history.
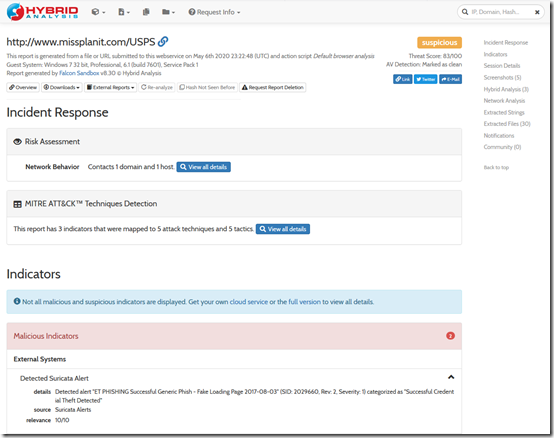
The site that loaded looked a little odd and then I noticed that the URL was not usps.com but something else. I quickly closed the browser tab. After confirming with the real USPS site that I did not miss a package and that the tracking number was bad, I checked the URL with www.VirusTotal.com. It came back 100% clean. Then I uploaded the URL to the helpful www.hybrid-analysis.com, which loads the page in Windows 7 and watches what happens. After several minutes, it came back with a detailed report that identified several suspicious indicators, including a “Suricata Alert”: “Detected alert “ET PHISHING Successful Generic Phish – Fake Loading Page 2017-08-03” (SID: 2029660, Rev: 2, Severity: 1) categorized as “Successful Credential Theft Detected”. The Threat Score is 83/100.
I did not enter any credentials so I think I’m okay, but looking at the email in more detail, I should have known better. It’s not awful—many of the links are to the real usps.com site—but it does have some poor English and the big giveaway, hovering over a link (without clicking) shows you that the link goes to a non-USPS site:
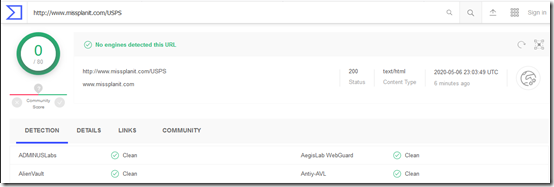
Here is the 100% clean VirusTotal analysis:
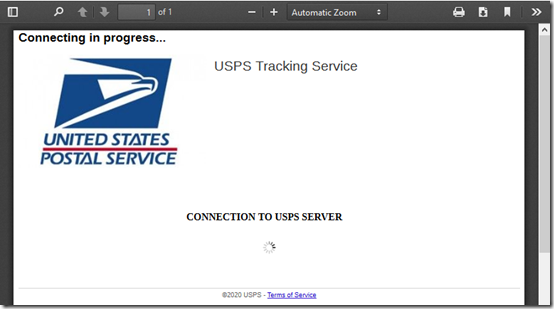
The www.screenshotmachine.com site was helpful in creating a PDF of what the site looks like, without having to load it myself. This is the “fake landing page” referred to above:
Finally, here’s the first part of the analysis from www.hybrid-analysis.com:


I love the Informed Mail service because it lets me know what to look for in my mailbox before I get it