Recently I was trying to get a Snom D785 phone to connect to a server that uses an SSL certificate issued by COMODO (now rebranded as Sectigo). Snom uses the Mozilla certificate list. So why does Firefox load the web site fine, but the phone fails with a certificate error?
Unlike Chrome and Internet Explorer, which use the computer’s certificate store, Firefox maintains its own list of trusted certificates.
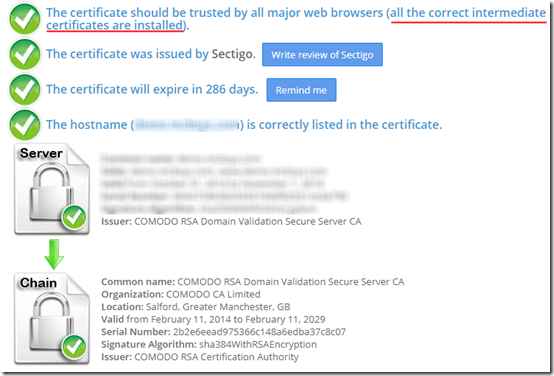
The issue comes down to the intermediate certificate. The web site certificate was issued by the “COMODO RSA Domain Validation Secure Server CA,” which was issued by the “COMODO RSA Certification Authority” root. The root is on the Mozilla list, but the intermediate certificate is not.
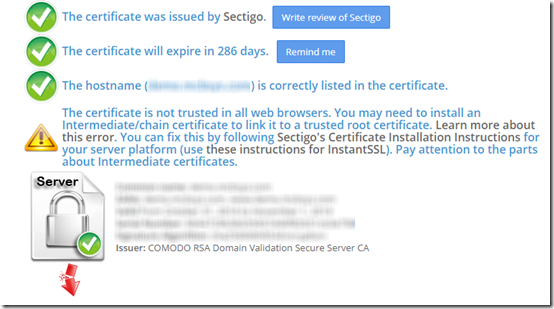
My first confirmation of the missing intermediate certificate came not from Firefox but from https://www.sslshopper.com/ssl-checker.html:
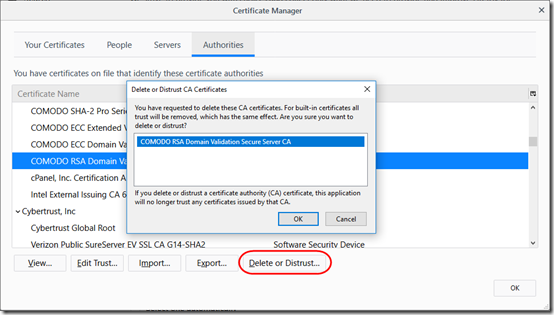
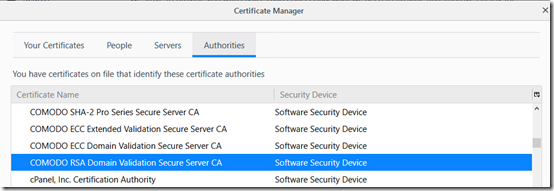
To test, in Firefox, I deleted the intermediate certificate from the Firefox Certificate Manager:
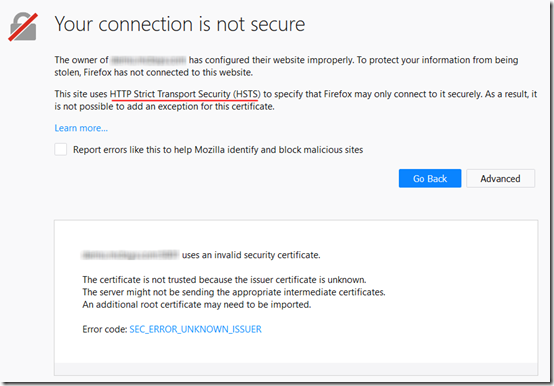
Now when I try to load the site in Firefox, it refuses. In fact, it won’t even let me add an exception, because the web site is configured to use HTTP Strict Transport Security (HSTS):
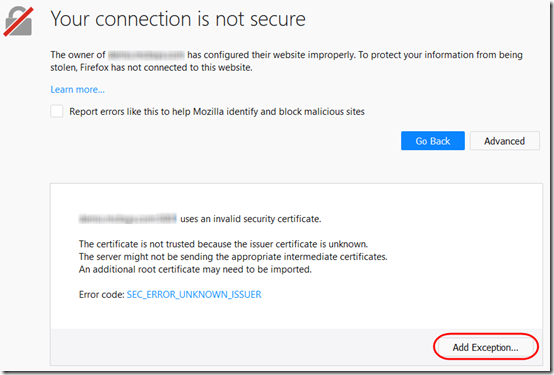
Using the information in this post, I disabled HSTS on the web server. Now Firefox would let me add an exception, but the exception would only be for the specific site; it does not trust the intermediate certificate:
I did not actually add the exception.
Next, I re-enabled HSTS and added the intermediate certificate to the web server. For nginx, this means a copy-and-paste of the intermediate certificate into the same file where the web server certificate is stored. As Mozilla’s configuration generator shows, in the server section, you need this line:
ssl_certificate /path/to/signed_cert_plus_intermediates;
In other words, point to one file containing all required public certificates.
Now, when I browse to that server in Firefox, it loads immediately. And here is the tricky bit: without any notification, Firefox re-loads the intermediate certificate into its certificate store:
That means that any site needing that intermediate certificate in the future will have it available. Put another way, if I browse to a site that includes the intermediate certificate, Firefox will load it, so that even if I later go to another site where the intermediate certificate is missing from the server, Firefox will still trust the site. See this StackExchange answer and its comments for more details.
Testing the site at this point using https://www.sslshopper.com/ssl-checker.html shows that intermediate certificate is available: