I’ve been using TrueCrypt for a while, and have recently switched to BitLocker. My main purpose is to encrypt backup disks that are taken off site, though I plan to use BitLocker for an internal data volume as well.
Recently a colleague noticed that a $495 program called Passware Kit Enterprise is claiming “Instant decryption of BitLocker To Go USB disks.” In fact they claim to be able to decrypt BitLocker and TrueCrypt disks, as well as PGP volumes. Really? How does that work? Are my efforts to encrypt sensitive data useless?
I should note that I am by no means a high-level security guru, but as an I.T. professional, I need to understand and advise customers on suggested best practices for mitigating security risks. Here’s what I found out in a few minutes of research on Passware and BitLocker.
Need a Live Memory Dump
This page at the Passware site describes the main prerequisite for decrypting a BitLocker or TrueCrypt volume: the target computer must be running and you must be able to get a full memory dump. This makes sense, since the key to decrypt the drive must be stored in memory while the computer is running.
The page lists three tools for getting the memory image:
– Passware FireWire Memory Manager (included in $795 Passware Forensic edition). This requires a FireWire port on the target machine. Oh no, my server doesn’t support FireWire! If yours does, take it out. Note that this could be a vulnerability on laptops.
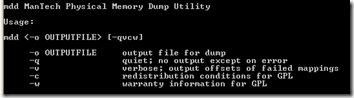
– Mantech Physical Memory Dump Utility. I downloaded this free tool from SourceForge and ran it. Based on the Usage instructions, it can only dump the memory of the current computer, and only if you are logged on as an administrator. If you can log on as an administrator, the BitLocker volume is probably already unlocked; you don’t really need to crack the password.
– Win32dd, now part of MoonSols Windows Memory Toolkit. I downloaded the free Community Edition of this tool and checked the command-line parameters. It appears more sophisticated than Mantech: it can run in client and server mode, allowing the client to send a dump across the network to the Win32dd server. But running the client would still require being logged on to the target machine.
Microsoft Response
This PC Magazine article includes a response from Microsoft about the Passware tool. Basically, it’s, “Yeah, we knew that.” To quote the quote, “We have always been up front in our discussions of Windows BitLocker and that it is intended to help protect data at rest (e.g. when the machine is powered off).”
For more arcane information about BitLocker that you ever wanted to know, see the Microsoft System Integrity Team Blog.
Conclusion
The rule of thumb with any full-disk encryption product seems to be for best protection, either prevent physical access to the machine (servers) or turn it off when not in use (laptops). Sleep is not enough; hibernation is probably okay. As long as the hacker does not have access to live system memory, they are stuck with a brute force attack on the volume, which could take a very long time.
Update March 2, 2011: Passware now claims here that if the system was hibernated, the BitLocker keys “could be possibly recovered from the hiberfil.sys file.” Failing that, they resort to brute force. So turn your computer completely off, don’t just hibernate it.
Update August 26, 2013: Elcomsoft Forensic Disk Decryptor also claims it can unlock Bitlocker. Their product page does a good job of explaining the prerequisites and includes a link to an open-source tool called Inception that is designed to exploit a FireWire vulnerability (IEEE 1394 SBP-2 DMA). Inception’s page, in turn, suggests mitigating the risk in Windows by blocking the SBP-2 driver as described in this Microsoft Knowledge Base article: Blocking the SBP-2 driver and Thunderbolt controllers to reduce 1394 DMA and Thunderbolt DMA threats to BitLocker.


Hi,
Does this mean that if I lost my memory stick with my account numbers and passwords on then that information can be ‘got off’ by some clever sod with the right software?
Will I have to buy ‘Pretty Good Privacy’ or is that also susceptible?
Many thanks for any tips.
David
The article above is more about encrypting system disks and when they may be vulnerable (if the PC is turned on when the hacker gets it). If the USB stick is lost without the computer, that would certainly be “data at rest,” so if it’s Bitlocker-encrypted, as far as I’ve been able to tell, it would be awfully hard to crack. There’s no harm in additionally using PGP to encrypt sensitive files, or for passwords, one of the password management programs that encrypts its password database.
I have a Secure Data folder on my Data drive which is separate from my system drive. I use folder lock. So after booting into Windows I then unlock my data folder. After finishing I lock the folder and shut down.
Seems to me from your article that Brute Force is the only way to access this and with my long complex key I expect that even a Botnet would need 50 years going at it.
Why anyone would want to encrypts their system drive is beyond me. Best practice is do not store any data on the system drive. The Microsoft Windows mish mash of system and data on C: drive makes it harder to organise your data and makes security more difficult.
Thanks for the useful article.
I use Bit Locker , one fear people have is losing the USB Stick containing the keys. I have a simple solution, I encrypt them my self ( using Acronis) and save them to http://WWW.DROPBOX.COM. Therefore if I visit a site and discover I have lost my USB stick , I can just download the keys , decrypt them using my own decryption program ( Acronis ) and place them on any USB key. Of course one must remember to destroy the “temporary” USB key after use.
Yes, keeping your keys secure but available is important. The “key” thing in your comment is that you encrypt them before uploading to Dropbox. If others are not aware, Dropbox itself is probably not secure:
Dropbox authentication: insecure by design
http://dereknewton.com/2011/04/dropbox-authentication-static-host-ids/
Also Dropbox can decrypt your files, e.g. under court order:
http://www.pcworld.com/businesscenter/article/228036/researcher_dropbox_misrepresents_security_features.html
I use a similar approach, encrypting a spreadsheet containing all my passwords, including BitLocker recovery keys, using PGP, and emailing the encrypted file to the guy who has Power of Attorney for me. For BitLocker, I additionally keep a duplicate USB key in the safety deposit box at my bank. Remember to test unlocking the drive by typing the recovery keys rather than having the USB key plugged in.
what happens if you loose your memory in an accident. you carnt even remember you had a safety deposit box let alone the key you used to encrypt the keys. You need to have access to your secret drive as your life depended on it.. what secure strategy is there for that one ah ??? common
As I said, my BitLocker keys (and all passwords) are held first by a trusted person, someone I’m in contact with regularly and who has legal authority (POA) to act on my behalf. As POA he knows my bank relationships and could have my box drilled if he couldn’t find the physical key. For BitLocker, he wouldn’t need to do that, because he already has a spreadsheet with all my passwords including the BitLocker keys. And when I send that spreadsheet to him, I encrypt it with his secure key (using PGP), so he can decrypt them using his own PGP private key.
Um… for Truecrypt, the encrypted drive must be mounted for it to work. You don’t have to turn off your computer, just unmount the drive when you’re not using it.
Rarf, I was thinking about the system drive of a Windows laptop when I suggested turning off the machine. If you have an encrypted secondary drive that you can unmount or disconnect, that should work too.
thanks for the quick breakdown of how it works, great article and easy to read. Also thanks for the update about hiberfil.sys. I will continue using truecrypt!!