Yesterday, Microsoft released this security advisory:
Vulnerability in Microsoft Video ActiveX control could allow remote code execution
That article includes a “Fix it” link that users can click on to disable the exploited ActiveX objects in Internet Explorer. The link downloads a small installer file which users can only execute if they are logged on as administrators. So deploying using that link would require that an administrator log on to each computer, including servers, and run the installer.
How can I quickly deploy this patch to all systems that I manage? I could follow the instructions in the related TechNet article to manually set up a .reg file, then deploy that with logon scripts or group policy. That article at least confirms that the fix is changing HKEY_LOCAL_MACHINE entries, so it’s not user-specific. I decided instead to deploy the installer using a Zenith job. Here’s how.
1. Make the Install File Accessible
1a. Download the 645KB MicrosoftFixit50287.msi from the article above.
1b. Upload it to a publicly-available web address.
2. Set Up the Zenith Job
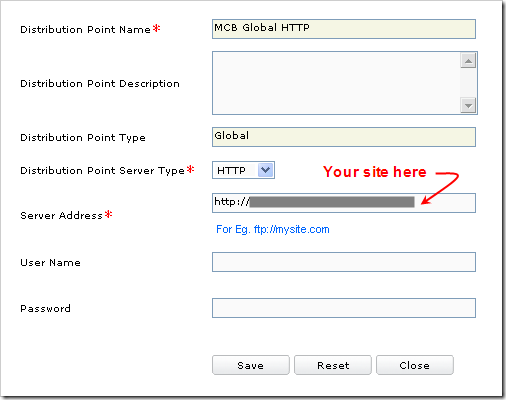
2a. If you don’t have a Global Distribution Point in Zenith yet, define one. In the Zenith portal, go to Job Management > Script Management > Distribution Points > Global and click on Create DP. Set up a link pointing to the location where you stored the file in step 1b:
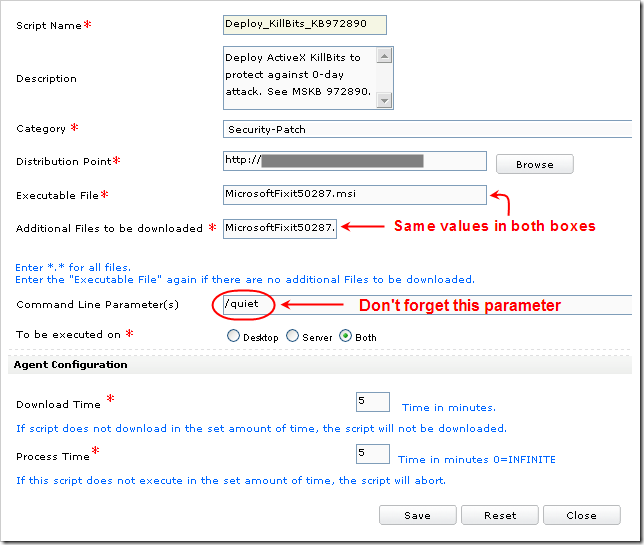
2b. Define the Zenith job. In the Zenith portal, go to Job Management > Script Management > Scripts > Global and click on Create Script. Fill in the fields as shown below.
- Choose any Category you like, or create your own.
- For the Distribution Point, select the location you defined in 2a.
- Make sure you put “MicrosoftFixit50287.msi” in both the Executable File and the Additional Files boxes.
- Make sure to specify the “/quiet” command line parameter, or the job will fail because no user interaction is possible.
3. Deploy the Job
You can deploy the script on one site or several.
3a. For testing, in the Zenith portal, go to Job Management > Script Management > Execute Scripts > Global, choose the Category you selected, choose the script, and follow the wizard to deploy it to one or two machines.
3b. After 15-30 minutes, in the Zenith portal, go to Job Management > Script Mgmt Report > Site Wise and check the execution status. When your test machines show “Success”, check the Event Log on the test machines. You should see the following success event in the Application Event Log:
Event Type: Information
Event Source: MsiInstaller
Event Category: None
Event ID: 11707
Date: 7/7/2009
Time: 12:11:00 PM
User: NT AUTHORITY\SYSTEM
Computer: TESTMACHINE
Description: Product: Microsoft Fix it 50287 — Installation completed successfully.
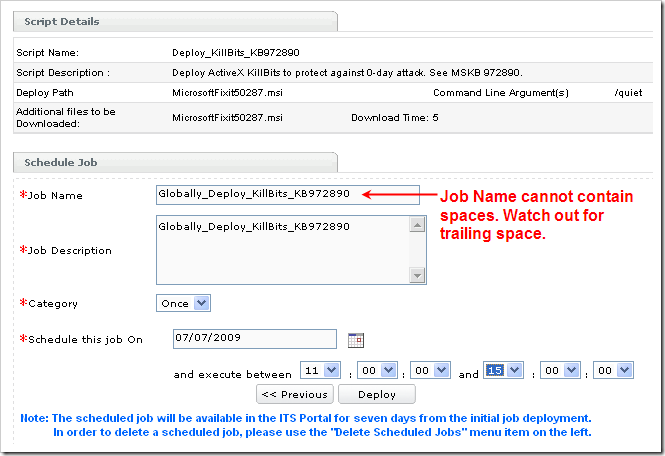
3c. Deploy globally. In the Zenith portal, go to Job Management > Script Management > Multi Site Job Deployment > Global Script, choose the script, and follow the wizard to deploy it to all Server and Desktop machines. (I didn’t see any issues when I re-deployed it to my test machines.) Set the time period long enough that it will include machines that are currently turned off. Your job definition should look something like this:
3d. Follow job progress. In the Zenith portal, go to Job Management > Script Management > Delete Scheduled Jobs. Under Multi Site Job Deployment: Scheduled Job Details, click on the job to see a list of all machines and their statuses. Once all the jobs complete, they will no longer be listed under Delete Scheduled Jobs; you’ll have to check individual sites under the Script Mgmt Report section.
Bigger Jobs
If you want to deploy other software with larger install packages, you may want to use local FTP distribution points rather than a global distribution point. I blogged about that here.
